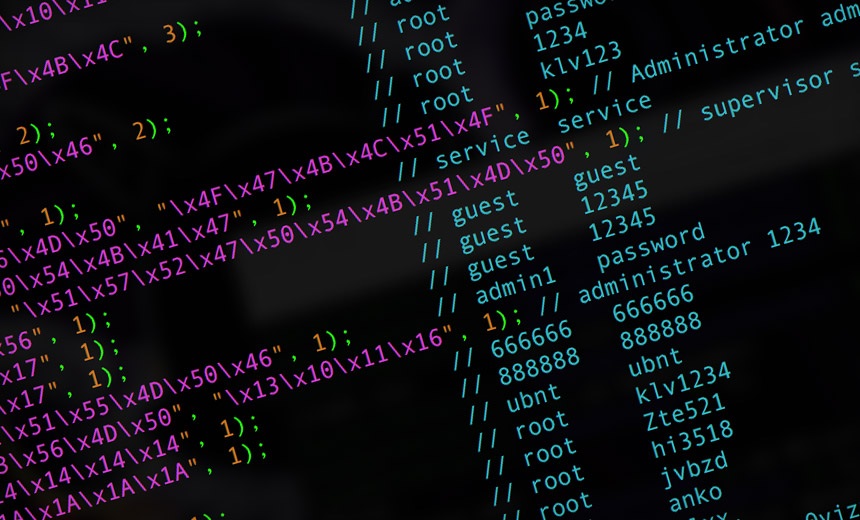
The growing prevalence of insecure Internet of Things (IoT) devices has opened major opportunities for IP booter panels to expand the scale and power of the distributed denial-of-service (DDoS) attacks they provide. By compromising connected cameras, smart home gadgets, routers, and more, booter services can build massive botnets capable of terabit floods. With estimates of over 20 billion IoT devices deployed globally, the sheer scale of insecure systems provides an unprecedented platform for booter-powered attacks. Critical flaws include:
- Default passwords – Manufacturers ship devices with easy default logins like “admin/admin”.
- No password requirement – Many IoT systems don’t force users to change defaults.
- Unpatched firmware – Vulnerable firmware often goes without security patches for years.
- Open access – IoT devices often expose telnet, SSH ports, and control panels to the internet.
- Weak protocols – Proprietary protocols lack encryption allowing eavesdropping and access.
These flaws leave IoT broadly exposed for attackers to gain control and infect with malware. And with new devices coming online every day, vulnerable systems keep piling up.
Building DDoS botnets
what is the best ip stresser? Leveraging security flaws, stresser/booter operators covertly compromise millions of IoT devices and assimilate them into powerful DDoS botnets. This provides direct bandwidth to barrage targets:
- Router botnets – Compromised home and SMB routers can generate floods up to 1Tbps.
- CCTV camera botnets – Infected surveillance camera networks wield incredible 1.5+ Tbps firepower.
- Printer botnets – Hacked enterprise printers can flood networks and cause costly outages.
- Smart home device botnets – Thermostats, appliances, and more make for large botnets.
- Network storage botnets – Breached NAS, DVRs, and DVDs are easily coerced into DDoS.
By exploiting an endless supply of neglected IoT devices, booters build and expand DDoS armies to sell as on-demand attack services.
Amplification DDoS attacks
In addition to comprising botnets, IoT devices also serve as amplification vectors for booter DDoS attacks:
- DNS amplification – Compromised home routers can be used as open resolvers for monstrous DNS floods.
- NTP amplification – Hackers reconfigure NTP on IoT devices to trigger amplification reflective attacks.
- SSDP amplification – The SSDP service on media devices amplifies traffic by 70x.
- CLDAP amplification – Exploiting misconfigured LDAP servers on enterprise IoT multiplies attack size.
- Memcached amplification – Unprotected memcached on IoT infrastructure provides 50x amplification.
Securing vulnerable IoT devices
While the scale of vulnerabilities makes IoT security a monumental challenge, steps can still be taken to significantly reduce risks:
- Enforce password requirements and defaults – Force users to replace simplistic admin passwords during initial setup.
- Issue firmware patches – Rapidly roll out updates to address known firmware-level exploits.
- Disable unnecessary services – Only run essential network services on IoT, deactivating things like telnet if not used.
- Implement strong authentication – Use multi-factor and certificates rather than just passwords for management access.
- Monitor for anomalies – Inspect network traffic and device configurations for indicators of compromise.
- Isolate IoT networks – Limit IoT device access to prevent wider pivoting by attackers.
- Inform users – Educate consumers and businesses about IoT hygiene and avoid devices with poor security track records.
While just basic precautions, these steps could eliminate the easiest IoT access vectors and vulnerabilities that IP booters rely on to enable devastating DDoS attacks.